Mindblown: a blog about philosophy.
-
Application Service Discovery – Week 7
I went through the ntopng code that I had mentioned last week, but I couldn’t gain a lot of information from it. So, I decided to dump it and proceed with writing code for my project.
-
Application Service Discovery – Week 6
Last week when I was trying to read data from packets, I came across a lot of garbled or unreadable data. I thought I could be unpacking the packets wrong, but I verified that I wasn’t. I realised that that data was just encrypted data and thus, unless I had the session keys as well, […]
-
Application Service Discovery – Week 5
After finishing a basic pcap parser that discovers web-servers running in a network, I wrote a simple wireshark-like program in python that can capture any packet either on the specified interface or on all interfaces.
-
Application Service Discovery – Week 4
After collecting data by using Wireshark, I started thinking of ways to identify services and hosts in the network.
-
Application Service Discovery – Week 3
I spent the past week learning about passive service discovery (PSD), and how it compares against active service discovery. PSD works on the principle of non-disruptive traffic analysis. In simpler words, it does not interfere in any way whatsoever with the traffic in the network and it is invisible to all the other hosts in […]
-
Application Service Discovery – Week 2
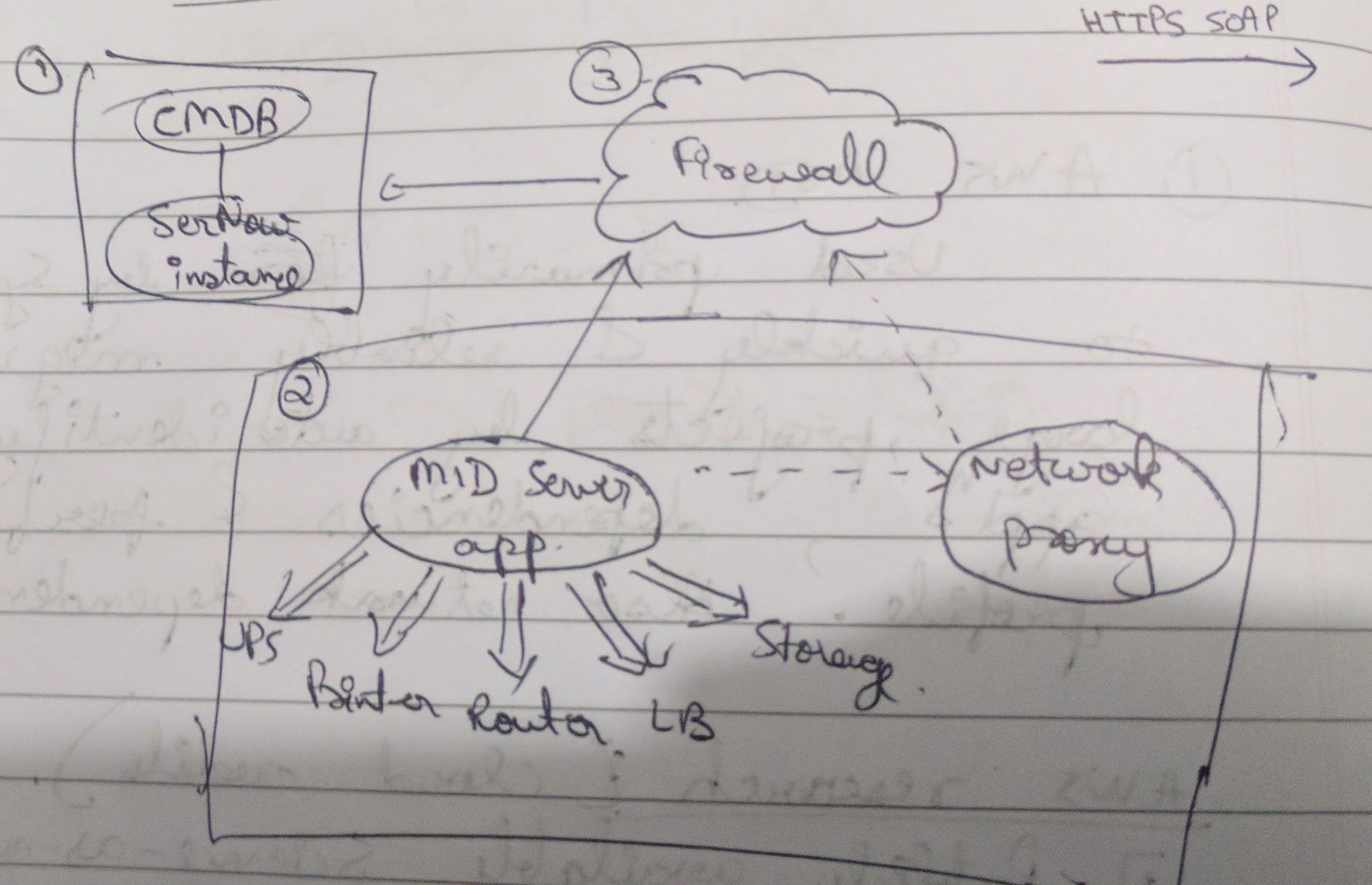
How does ServiceNow service discovery work? Agentless discovery Two parts: Communications Data collection and processing
-
Application Service Discovery – Week 1
DigitalOcean has an excellent series on The Docker Ecosystem, and part 3 of this series explains the general concepts of Application Service Discovery (ASD). I’d recommend it to anyone who has no clue what ASD is, and wants to understand it, from a fairly abstract point of view.
-
Hello world!
I’ll be writing about what I learn while doing my final year project which is based on application service discovery, and also take you through a journey of finding out which is the best biriyani in Bangalore!
Got any book recommendations?